How to Bulk Enable All Sentinel Analytic Rules (The Easy Way)

Alright, class, let's have an honest conversation.
You've just deployed Microsoft Sentinel. You followed the guides. You've connected your data sources from the content hub—Microsoft Defender, Entra ID, the whole glorious suite. You're feeling like a cybersecurity god. You can almost hear the angels singing as you navigate to the Analytics blade, ready to unleash a fury of threat detections upon your unsuspecting logs.
And then you see it.
Hundreds. Hundreds of analytic rule templates, all sitting there, inert, with a smug little "In use: 0" next to their names. And you realise the horrible truth. Microsoft, in its infinite wisdom, requires you to click into each one, click "Create," click "Next," "Next," "Next," and finally "Create"
For every single rule.

It's the digital equivalent of being given a sports car but having to assemble the engine yourself with a tiny Allen key. It's soul-destroying. It's a one-way ticket to carpal tunnel and questioning all your life choices.
What if I told you there’s a better way? What if I told you we could do in three minutes what would normally take three hours of mind-numbing clicking?
Well, buckle up. Today, we're fighting back with the most powerful weapon in an admin's arsenal: a glorious, beautiful, slightly intimidating PowerShell script.
The Problem: Why Can't I Just "Enable All"?
Before we get to the magic, let's understand the "why." Why is this so tedious? When you install a "Solution" from the Sentinel Content Hub, you're not actually installing active rules. You're installing templates. Think of them as blueprints. Sentinel generously gives you the blueprints for 50 different types of security alarms but then expects you to walk around and install each one by hand.
This is fine for one or two. It's a nightmare for 200. Not everyone will have access to exported Analytic Rules, or centralised systems like Terraform, DevOps or Workspace Manager. You'd need to hire an intern whose only job is to click "Next."
The Solution: Let the Robot Do the Clicking
I got tired of this nonsense, so I built a robot to do the work for me. This PowerShell script connects to your Sentinel workspace, finds every single analytic rule template from every solution you've installed, and creates an active (or disabled) rule from it.
And the best part? It preserves all the MITRE ATT&CK mappings. You get all the detection power without any of the manual labour.
What You'll Need (The Prerequisites)
Don't panic. This isn't as scary as it looks. You just need two things:
- The Right Permissions (The Bouncer at the Club): You can't just walk in and start changing things. You need to have the right access level. Specifically, the Microsoft Sentinel Contributor role on your workspace.
The Azure PowerShell Module: If you don't have it, it's one simple command. Fire up Azure CLI >_ in the top navigation bar. Then run this:
Install-Module -Name Az -Force -AllowClobberThat's it. You're ready.
The Script: Your New Best Friend
Here it is. The code that will save your sanity. You can grab the latest version from my GitHub repo here.
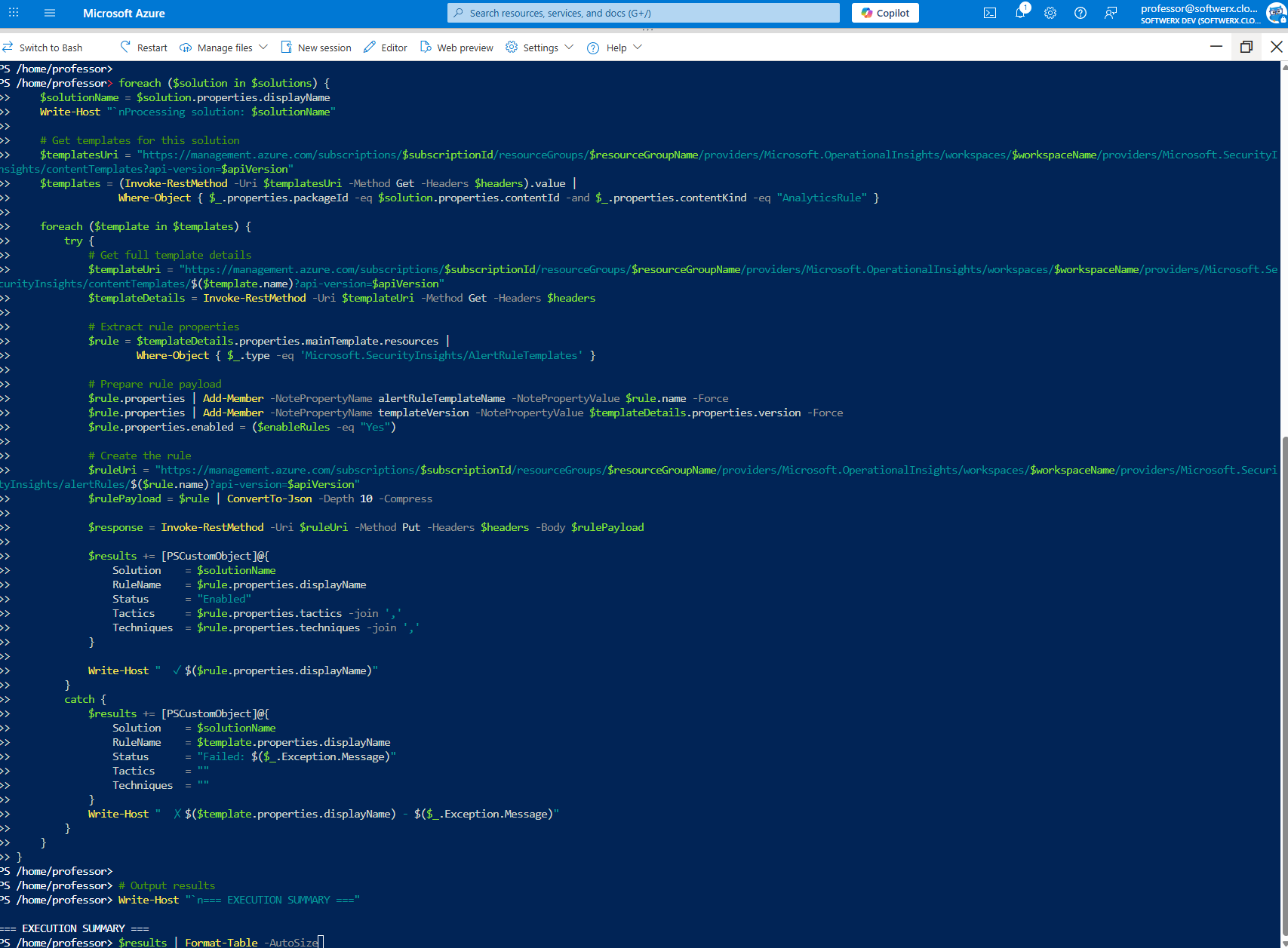
<#
.SYNOPSIS
Enable ALL Microsoft Sentinel Analytics Rules from ALL sources
With guaranteed API version compliance and MITRE ATT&CK preservation
#>
# Your environment parameters
$subscriptionId = "<subscription ID>"
$resourceGroupName = "<Resource_Group_Name>"
$workspaceName = "<Log_Analytics_Workspace_Name>"
$enableRules = "Yes" # "Yes" to enable, "No" to create disabled
# API Configuration
$apiVersion = "2024-10-01-preview" # Supports MITRE ATT&CK sub-techniques
# Get auth token using Azure CLI (already logged in via `az login` or Cloud Shell)
$token = az account get-access-token --resource "https://management.azure.com" --query accessToken -o tsv
$headers = @{
'Authorization' = "Bearer $token"
'Content-Type' = 'application/json'
}
# Get all content packages
$contentUri = "https://management.azure.com/subscriptions/$subscriptionId/resourceGroups/$resourceGroupName/providers/Microsoft.OperationalInsights/workspaces/$workspaceName/providers/Microsoft.SecurityInsights/contentProductPackages?api-version=$apiVersion"
$solutions = (Invoke-RestMethod -Uri $contentUri -Method Get -Headers $headers).value
$results = @()
foreach ($solution in $solutions) {
$solutionName = $solution.properties.displayName
Write-Host "`nProcessing solution: $solutionName"
# Get templates for this solution
$templatesUri = "https://management.azure.com/subscriptions/$subscriptionId/resourceGroups/$resourceGroupName/providers/Microsoft.OperationalInsights/workspaces/$workspaceName/providers/Microsoft.SecurityInsights/contentTemplates?api-version=$apiVersion"
$templates = (Invoke-RestMethod -Uri $templatesUri -Method Get -Headers $headers).value |
Where-Object { $_.properties.packageId -eq $solution.properties.contentId -and $_.properties.contentKind -eq "AnalyticsRule" }
foreach ($template in $templates) {
try {
# Get full template details
$templateUri = "https://management.azure.com/subscriptions/$subscriptionId/resourceGroups/$resourceGroupName/providers/Microsoft.OperationalInsights/workspaces/$workspaceName/providers/Microsoft.SecurityInsights/contentTemplates/$($template.name)?api-version=$apiVersion"
$templateDetails = Invoke-RestMethod -Uri $templateUri -Method Get -Headers $headers
# Extract rule properties
$rule = $templateDetails.properties.mainTemplate.resources |
Where-Object { $_.type -eq 'Microsoft.SecurityInsights/AlertRuleTemplates' }
# Prepare rule payload
$rule.properties | Add-Member -NotePropertyName alertRuleTemplateName -NotePropertyValue $rule.name -Force
$rule.properties | Add-Member -NotePropertyName templateVersion -NotePropertyValue $templateDetails.properties.version -Force
$rule.properties.enabled = ($enableRules -eq "Yes")
# Create the rule
$ruleUri = "https://management.azure.com/subscriptions/$subscriptionId/resourceGroups/$resourceGroupName/providers/Microsoft.OperationalInsights/workspaces/$workspaceName/providers/Microsoft.SecurityInsights/alertRules/$($rule.name)?api-version=$apiVersion"
$rulePayload = $rule | ConvertTo-Json -Depth 10 -Compress
$response = Invoke-RestMethod -Uri $ruleUri -Method Put -Headers $headers -Body $rulePayload
$results += [PSCustomObject]@{
Solution = $solutionName
RuleName = $rule.properties.displayName
Status = "Enabled"
Tactics = $rule.properties.tactics -join ','
Techniques = $rule.properties.techniques -join ','
}
Write-Host " ✓ $($rule.properties.displayName)"
}
catch {
$results += [PSCustomObject]@{
Solution = $solutionName
RuleName = $template.properties.displayName
Status = "Failed: $($_.Exception.Message)"
Tactics = ""
Techniques = ""
}
Write-Host " ✗ $($template.properties.displayName) - $($_.Exception.Message)"
}
}
}
# Output results
Write-Host "`n=== EXECUTION SUMMARY ==="
$results | Format-Table -AutoSize
How to Use This Beast (It's Easier Than It Looks)
Step 1: Fill in the Blanks
Open the script in your favourite editor (VS Code, PowerShell ISE, or even Notepad if you're a monster). At the very top, you'll see four lines you need to edit.
$subscriptionId: Your Azure Subscription ID.$resourceGroupName: The name of the resource group where your Sentinel workspace lives.$workspaceName: The name of your Sentinel Log Analytics Workspace.$enableRules: Set this to"Yes"to turn the rules on immediately.
Step 2: Run It
Copy the entire script. You can run this from your local machine, but the easiest way is to use the Azure Cloud Shell.
- Log in to the Azure Portal.
- Click the little command line icon
>_in the top navigation bar. - When the shell opens, make sure it's set to PowerShell.
- Paste the entire script into the Cloud Shell and hit Enter.
Step 3: Grab a Coffee and Watch the Magic
You'll see the script churning through each solution, finding the templates, and creating the rules one by one.
Processing solution: Microsoft Defender XDR (This just means the rule already exists, no biggie!)
✓ TI Map IP entity to Kaskela...
✓ Creation of incidents from Microsoft Defender XDR...
Processing solution: Azure Active Directory
✓ Rare and suspicious sign-ins...
✗ Some other rule - Failed: (409) Conflict
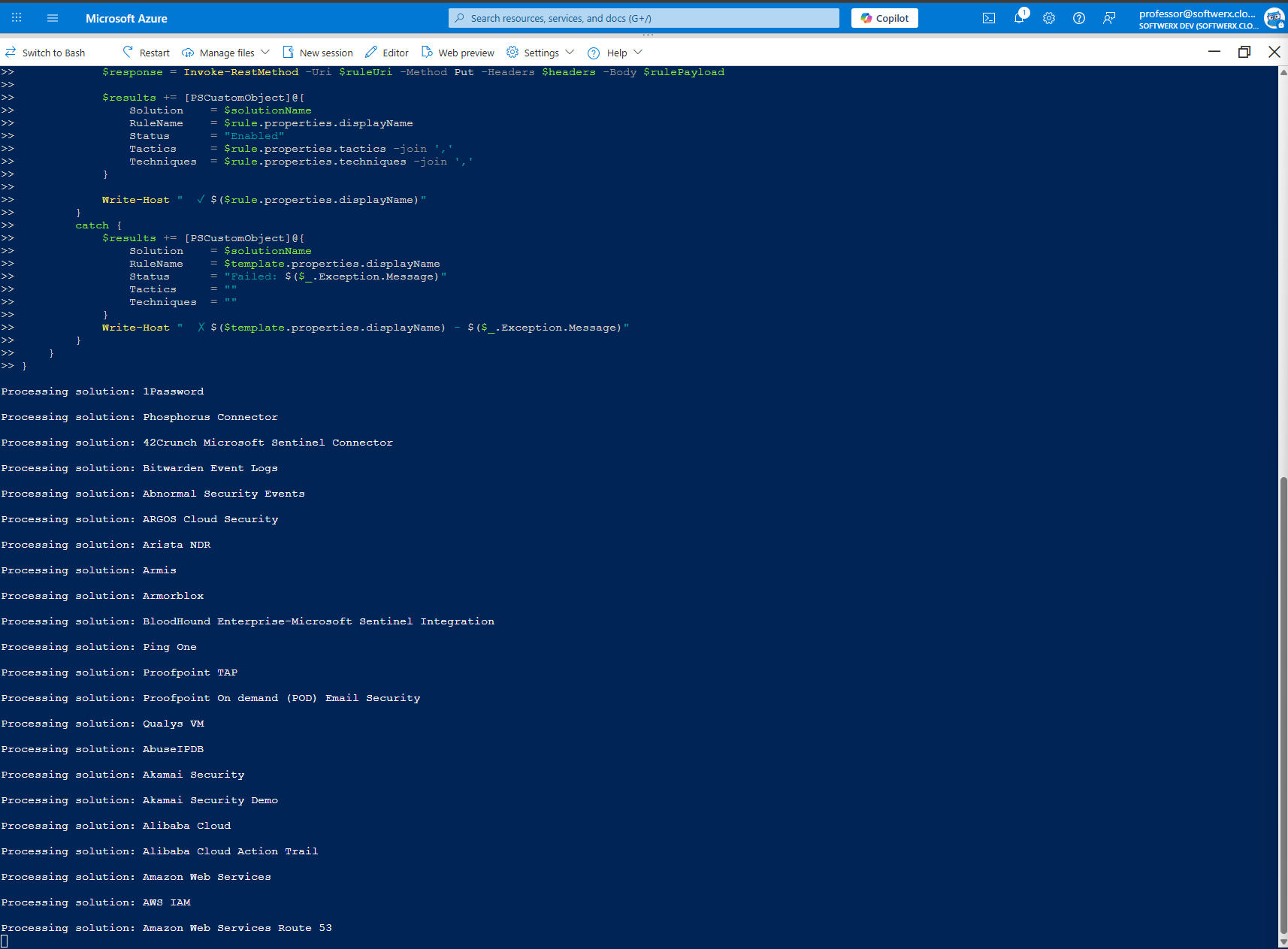
Every time it finds a solution, it will start processing it and enabling Analytic Rules.
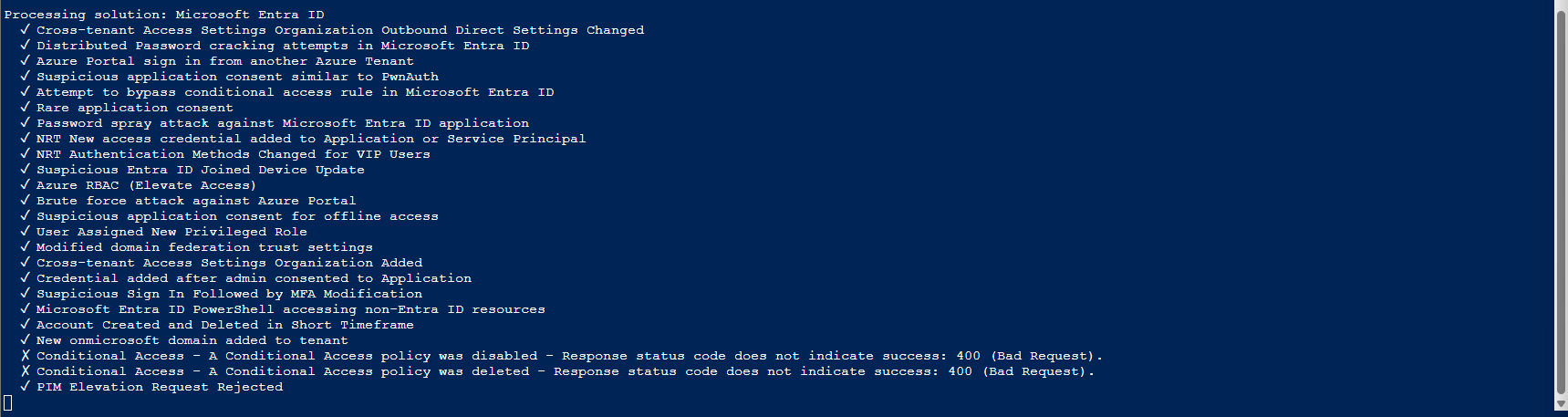
When it's done, you'll have a beautiful summary table showing you what was enabled.
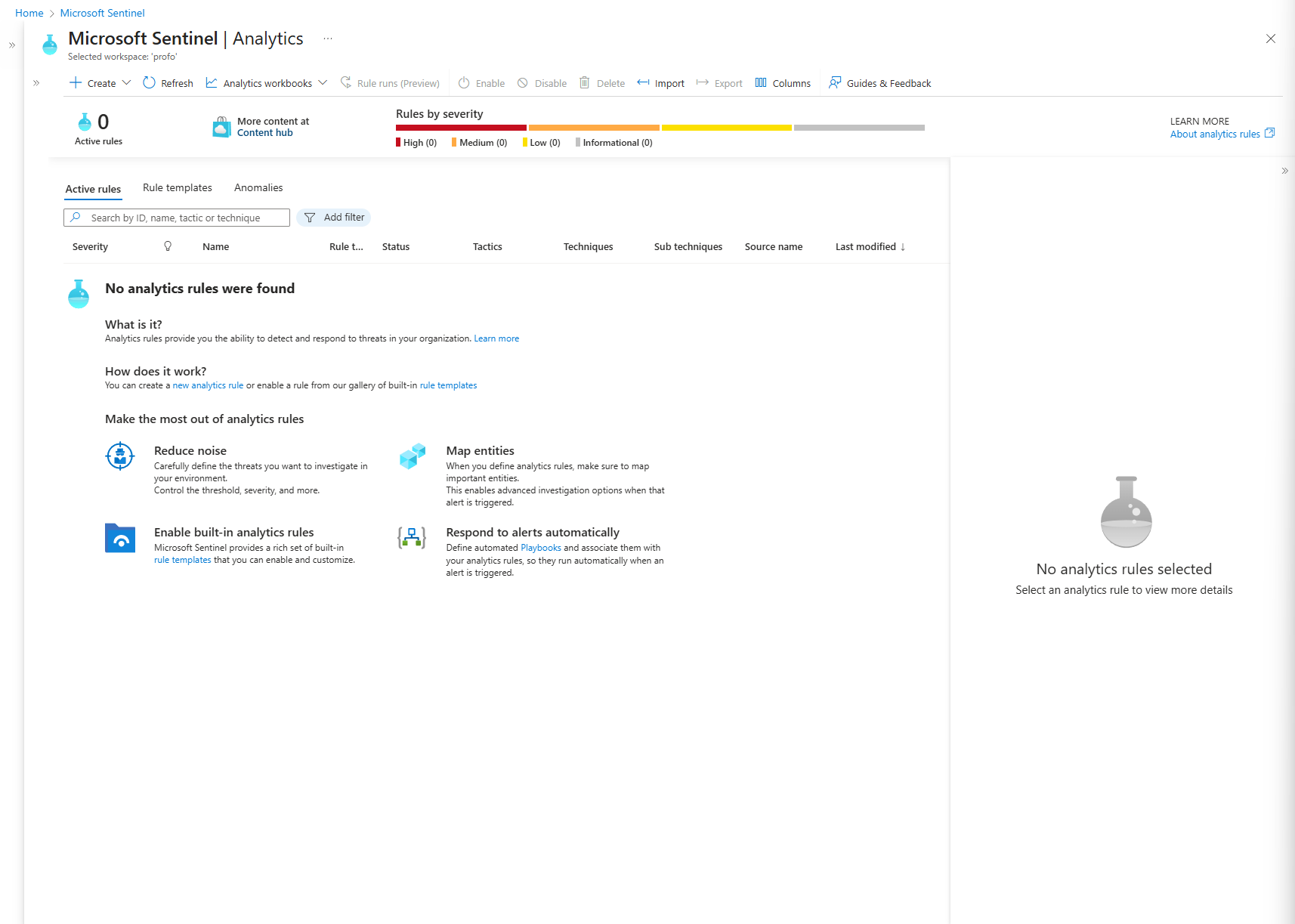
Just look at this beauty! Before running the script:
After:
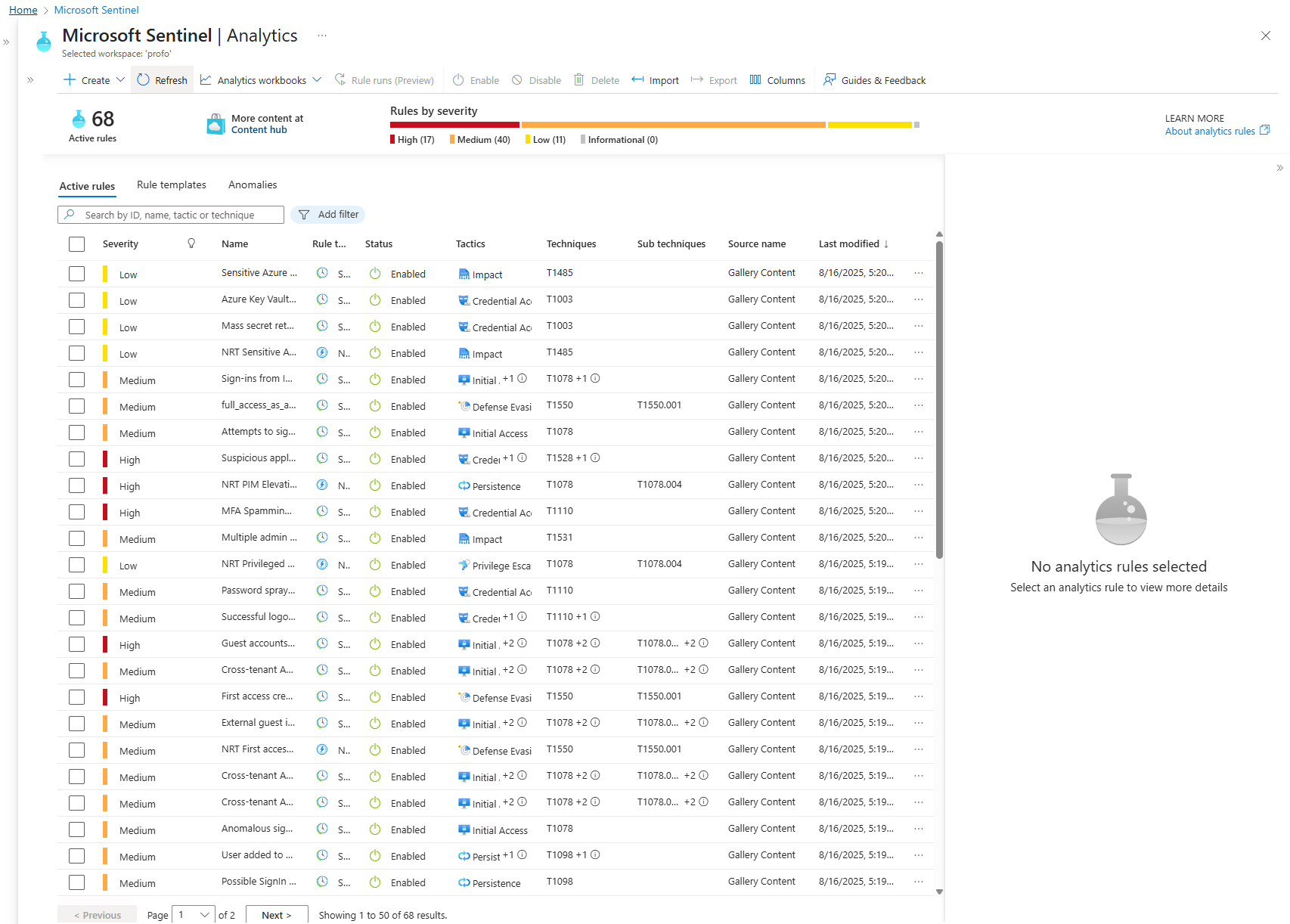
You just did hours of work in minutes. That, class, is what working smarter, not harder, is all about. Now go show your boss and ask for a raise, soldier.
