Microsoft Sentinel's Secret Weapon: Your First Watchlist

Alright, class.
You've got your Sentinel instance running. It’s like a sprawling, open-world RPG. You’ve learned the basic controls (incident investigation), you’ve equipped your first abilities (analytic rules), and you’ve even learned a few magic spells (KQL).
But your world map is still blank. Everything looks the same. An alert for the intern's laptop looks identical to an alert for your CEO's workstation. Sentinel doesn't know what's a low-level mob is and what's a raid boss.
Today, we fix that. We're going to give Sentinel a cheat sheet. A list of all the VIPs, the high-value loot, and the quest-critical items in your environment.
Welcome to the world of Watchlists.
Why Bother With a Watchlist? It's Your "Mark Target" Ability
A Watchlist is exactly what it sounds like: a list of things you want to keep a special eye on. Think of it as painting a giant, glowing target on certain entities in your environment. This list gives Sentinel critical business context it would never have on its own.
What kind of stuff goes on a watchlist?
- VIP Users: Your C-suite (CEO, CTO, CFO). An incident involving one of them is an immediate "drop everything and look at this" moment.
- High-Value Assets: Domain controllers, critical production servers, the database that holds all the secret sauce.
- Terminated Employees: The insider threat is real. When someone leaves, especially if it wasn't on good terms, you want to know immediately if their account shows any sign of life.
- Service Accounts: You want to know if a non-interactive service account suddenly has an interactive logon.
- Suspicious Users: Maybe you have an employee on a performance plan or someone you suspect is up to no good. A watchlist lets you monitor their activity without tipping them off.
When an incident fires and the user, IP, or hostname involved is on one of these lists, you can automatically escalate its priority. It's the difference between a random boar encounter and the dragon guarding the main quest line.
Weapon Crafting: Forging Your CSV File
Before we can do anything in Sentinel, we need to create our list. The easiest way to start is with a CSV (Comma-Separated Values) file. Don't let the name scare you; it's just a simple text file that uses commas to separate columns. It's the universal language of spreadsheets.
Method 1: The Notepad Way (Quick and Dirty)
- Open Notepad on your machine.
- The very first line must be your column headers, separated by commas. No spaces after the commas.
- On the next lines, add your data, making sure the values line up with the headers.
- Save the file with a
.csvextension (e.g.,InsiderRisk.csv). Make sure to change "Save as type" to "All Files" so it doesn't save as a .txt file.
Here is the exact text to copy and paste for our insider risk scenario:
UserPrincipalName,DeviceName,Notes
bob.smith@itprofessor.cloud,BOB-LAPTOP-01,"Potential risk. Monitoring for data exfiltration."
jane.doe@itprofessor.cloud,JANE-DESKTOP-03,"Suspicious activity reported by manager."Output
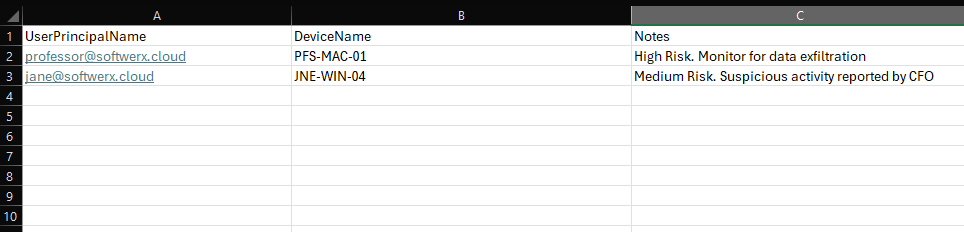
Method 2: The Excel Way (Clean and Organized)
- Open Microsoft Excel.
- In the first row, enter your column headers in separate cells (A1, B1, C1, etc.).
- Fill in the data underneath the appropriate headers.
- Go to File > Save As.
- In the "Save as type" dropdown, select CSV (Comma delimited) (*.csv). This is crucial.
- Give it a name and save it. Excel might give you a warning about losing features; just click "Yes."
Now that you have your enchanted scroll (the CSV file), we're ready to upload it to Sentinel.
Our First Quest: Creating the Insider Risk Watchlist
- In the Azure Portal, navigate to your Microsoft Sentinel workspace.
- On the left-hand menu, under Configuration, click Watchlist.
- Click the shiny + Add new button at the top. This opens the Watchlist wizard.
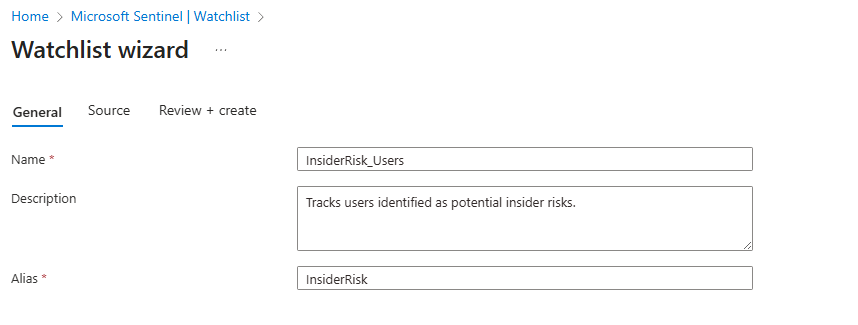
Basics Tab:
- Name: Give it a descriptive name. Let's use
InsiderRisk_Users. - Alias: This is the most important name. It's the short name you will use in all your KQL queries. It cannot have spaces. Let's use
InsiderRisk. - Description: Be a good teammate and write a short sentence about what this list is for. "Tracks users identified as potential insider risks."
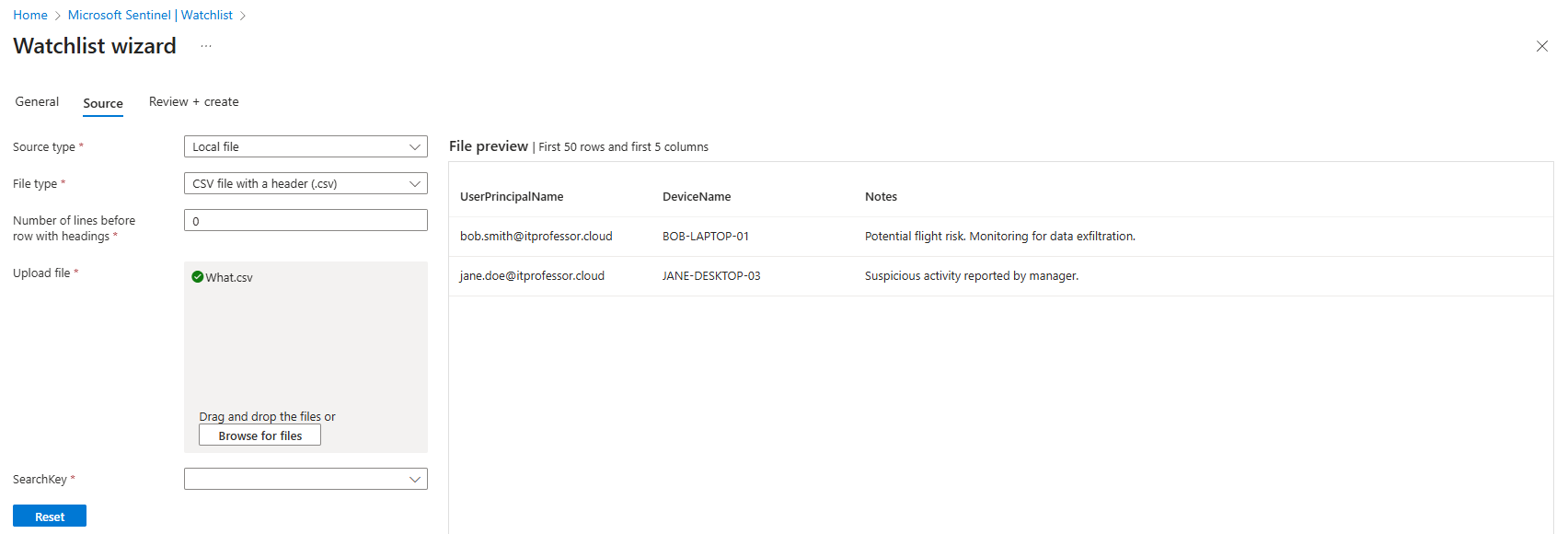
Source Tab:
- Leave the Watchlist source type as Local file.
- Click the Browse for files button and upload the
InsiderRisk.csvfile you just created. - SearchKey: This is the "join key". It's the one piece of data that will link our static watchlist to the dynamic logs flowing into Sentinel. Since we want to track user activity, our
SearchKeymust beUserPrincipalName. This is because tables likeSigninLogsandOfficeActivityalso have aUserPrincipalNamecolumn (and we want to use those tables in future detections)
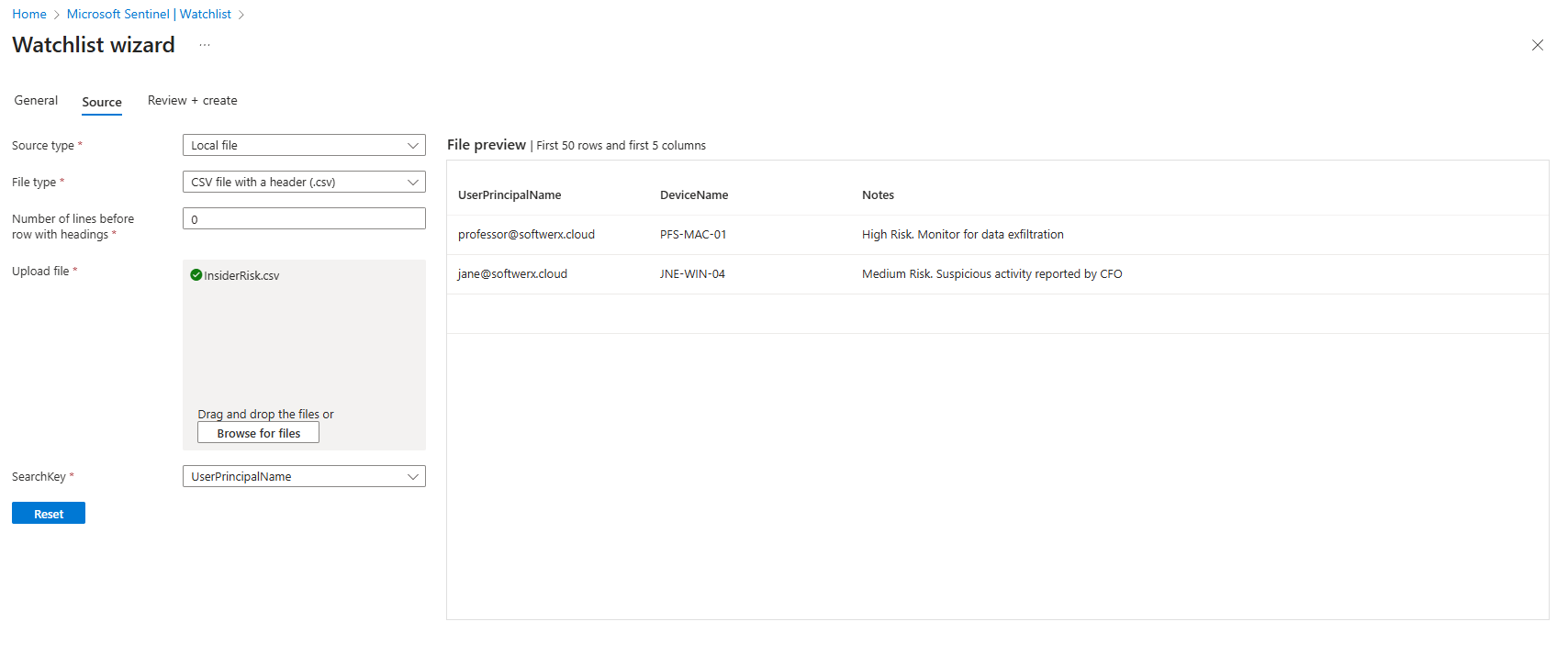
- Click Next, review your settings on the final tab, and click Create.
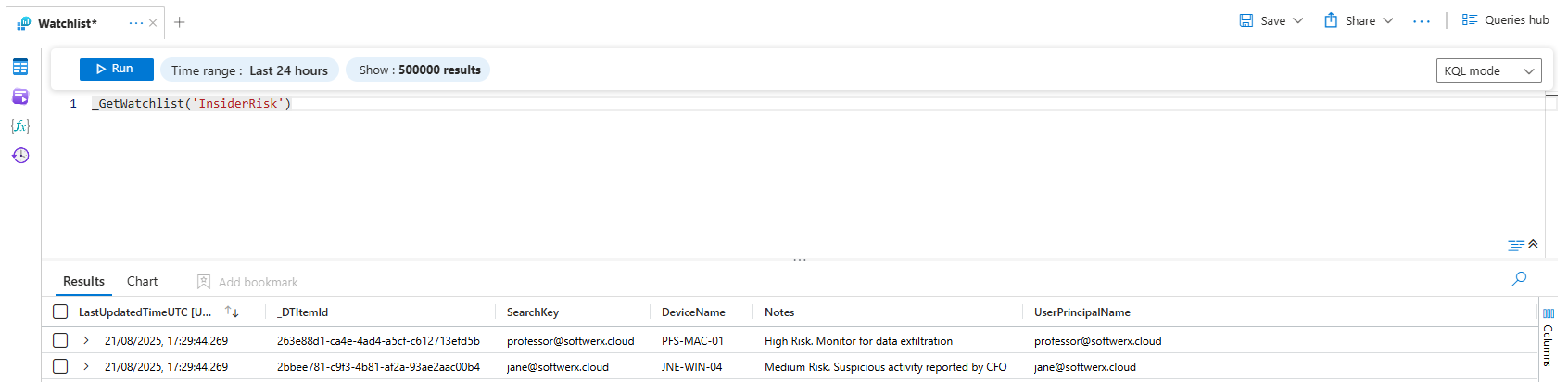
It can take a few minutes for the data to be available. Once it's done, you can click on your new watchlist, select View in Logs, and see the data you just uploaded, neatly formatted in a table.
Keeping Your List Fresh: Manual vs. Automated Buffs
Your watchlist is just a list. You can edit it manually anytime by going into the watchlist, clicking "Edit watchlist items", and adding, editing, or deleting rows.
But the real endgame is automating it. In a future post, we’ll build a Logic App that acts as a quest-giver. For example: "When a user is added to the 'Terminated Employees' group in Entra ID, automatically add them to this watchlist." For now, manual updates are perfectly fine for getting started.
The Hunt is On: Using Your Watchlist in KQL
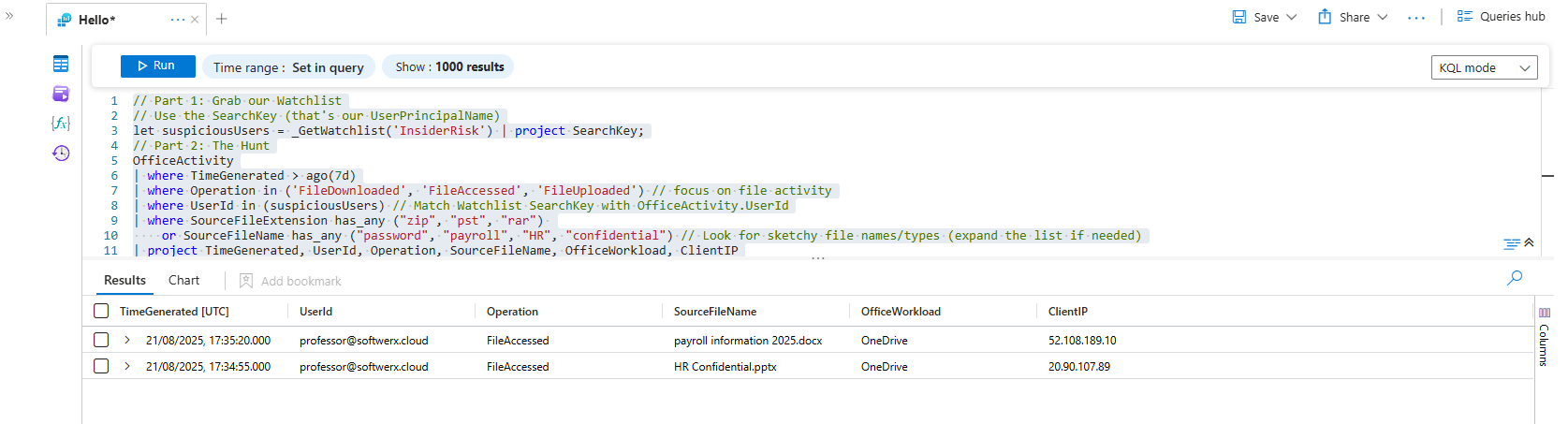
Alright, our watchlist is armed and ready. Let's use it to hunt. We suspect the user might be trying to download sensitive company files. We want to see if he's accessing anything in SharePoint with juicy keywords in the file name.
Open up Logs and let's write our KQL
// Part 1: Grab our Watchlist
// Use the SearchKey (that's our UserPrincipalName)
let suspiciousUsers = _GetWatchlist('InsiderRisk') | project SearchKey;
// Part 2: The Hunt
OfficeActivity
| where TimeGenerated > ago(7d)
| where Operation in ('FileDownloaded', 'FileAccessed', 'FileUploaded') // focus on file activity
| where UserId in (suspiciousUsers) // Match Watchlist SearchKey with OfficeActivity.UserId
| where SourceFileExtension has_any ("zip", "pst", "rar")
or SourceFileName has_any ("password", "payroll", "HR", "confidential") // Look for sketchy file names/types (expand the list if needed)
| project TimeGenerated, UserId, Operation, SourceFileName, OfficeWorkload, ClientIP
| sort by TimeGenerated desc
And bang. The results pop up. You can see that user accessed payroll information 2025 and HR Confidential files. The trap worked. The target we painted just lit up like a Christmas tree.
That, class, is the power of a watchlist. You've just transformed Sentinel from a generic alarm system into a context-aware security machine that understands your environment, its raid bosses, and its most valuable loot. You’ve given it the intelligence to know what truly matters.
Now go forth and mark your targets. Class dismissed.
