Microsoft Sentinel: Let the Robots Do the Work - Your First Automation Playbook

Alright, class, let's talk about burnout. Specifically, the burnout that comes from the first five minutes of every single incident. A high-severity alert fires. Now what? Who's taking it? Is it assigned yet? You refresh the queue, wondering if anyone else has seen it. It's a soul-crushing cycle of clicks just to get an incident from 'New' to 'Active'. For the SOC person working alone, it's a constant context switch that kills your focus.
What if I told you that you could automate that first, critical step? What if you could take the "who owns this?" chaos and turn it into a one-click process, right inside Microsoft Teams?
Welcome to the world of Automation in Microsoft Sentinel. This is the "SOAR" (Security Orchestration, Automation, and Response) that everyone on LinkedIn talks about, but without the confusing buzzwords. In simple terms, this is how you get your time back. It's how you eliminate the initial triage delay and focus on what actually matters: hunting threats.
So, buckle up and top up that coffee. We're about to build a robot butler for your SOC.

Automation: What It Is and Why You Should Care
In Sentinel, automation comes in two main flavours:
- Automation Rules: These are simple, "if-this-then-that" rules that run inside Sentinel. They are great for basic triage. For example: "IF a new incident is created for
Brute Force Attempts, AND the source IP is1.2.3.4(your known test IP), THEN automatically close the incident as aBenign Positive." It's a quick and easy way to handle known, noisy alerts. - Playbooks (Logic Apps): This is the main event. A Playbook is a visual workflow built on Azure Logic Apps. It's a series of steps that can interact with services both inside and outside of Azure. Think of it as a digital flowchart that can act like a junior analyst. It can enrich data, post notifications, create service desk tickets, and even take action like blocking an IP or disabling a user.
Today, we're building a Playbook that will change your team's workflow forever.
Our Mission: The "SOC Triage Bot" in Microsoft Teams
We're going to build a playbook that does the following:
- When a new, high-severity incident is created in Sentinel...
- It will automatically post a detailed "Adaptive Card" in a specific Teams channel.
- The card will wait for an analyst to respond by clicking a button: "Take Ownership" or "Dismiss."
- Based on the response, the playbook will update the incident in Sentinel—assigning the owner and setting the status to "Active."
- Adaptive card will contain a link that can be used to directly open the incident in Sentinel.
This is amazing stuff. It brings the incident triage process directly into the tool where your team already communicates, and it's just the beginning of fantastic things you can use it for!
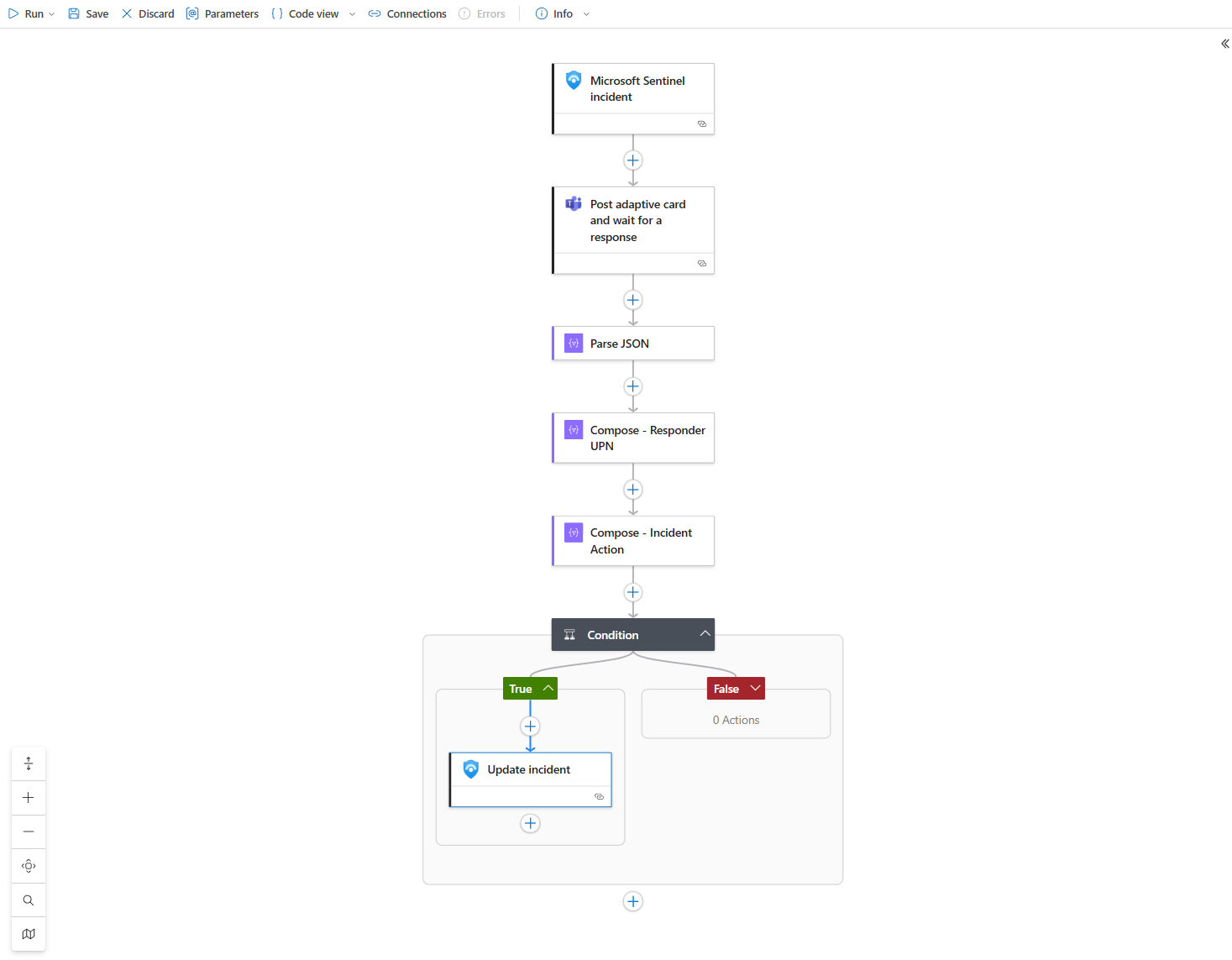
Step 1: Building the Logic App (The Robot's Brain)
First, we need to build the Logic App itself.
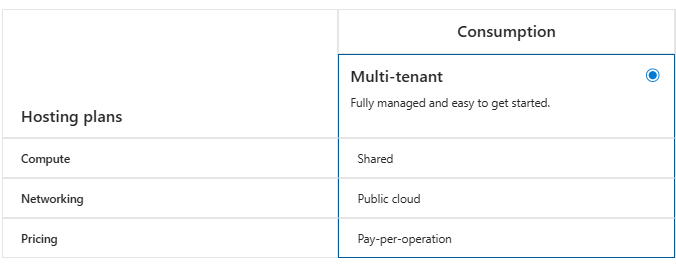
- In the Azure Portal, search for "Logic App" and click "Add."
- Create a new Consumption plan Logic App. Give it a descriptive name like
My-Life-Is-A-Failure.
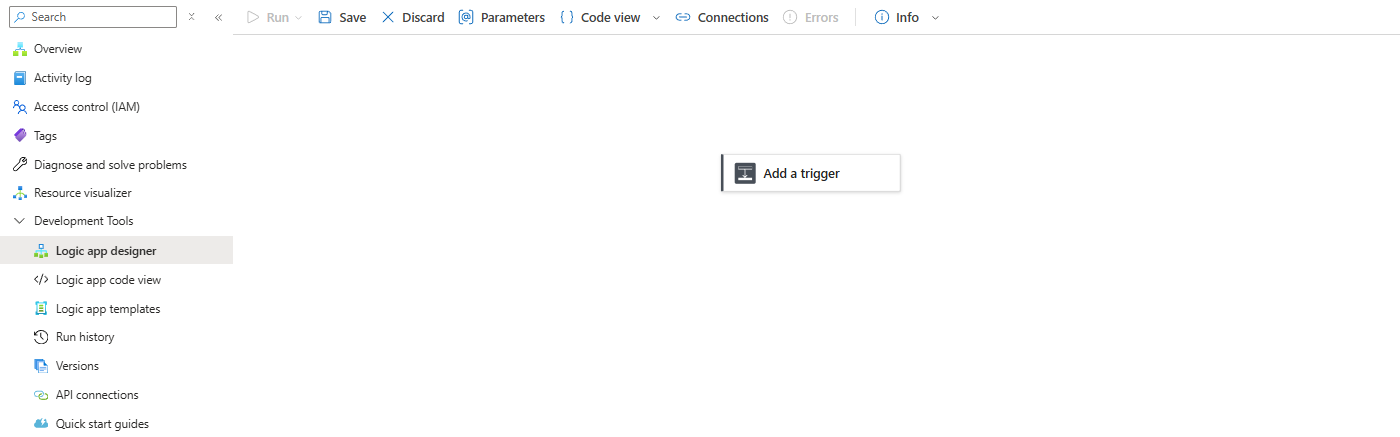
- Once it's deployed, go to the Logic App and open the Logic App Designer. We're starting with this blank canvas.
Step 2: The Trigger - "When an Incident is Created"
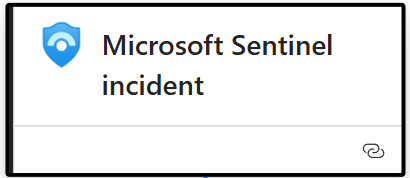
Every playbook needs a trigger. Search for "Microsoft Sentinel" and select the trigger: "Microsoft Sentinel incident" The first time you do this, it will ask you to sign in and create an API connection. This is normal; you're just giving your playbook permission to talk to Sentinel.
Step 3: The Action - "Post an Adaptive Card and Wait"
This is the core of our playbook.
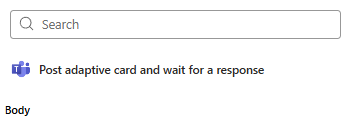
- Click "+ New step" and search for "Microsoft Teams."
- Select the action: "Post adaptive card and wait for a response."
- Configure the action:
- Post as: Flow bot
- Post in: Channel
- Message: This is where we paste our Adaptive Card JSON code. This code defines how the card will look in Teams.
- Team: Select your Team channel
- Channel: Select your Channel
{
"$schema": "http://adaptivecards.io/schemas/adaptive-card.json",
"type": "AdaptiveCard",
"version": "1.4",
"body": [
{
"type": "ColumnSet",
"columns": [
{
"type": "Column",
"width": "auto",
"items": [
{
"type": "Image",
"url": "https://www.itprofessor.cloud/content/images/size/w960/2025/08/PROFOHACKER.png",
"size": "Medium",
"style": "Person"
}
]
},
{
"type": "Column",
"width": "stretch",
"items": [
{
"type": "TextBlock",
"text": "New Sentinel Incident",
"weight": "Bolder",
"size": "Large"
},
{
"type": "TextBlock",
"text": "Incident #: @{triggerBody()?['object']?['properties']?['additionalData']?['mergedIncidentNumber']}@{triggerBody()?['object']?['properties']?['incidentNumber']}",
"spacing": "None",
"isSubtle": true,
"wrap": true
}
]
}
]
},
{
"type": "FactSet",
"facts": [
{
"title": "Title:",
"value": "@{triggerBody()?['object']?['properties']?['title']}"
},
{
"title": "Severity:",
"value": "**@{triggerBody()?['object']?['properties']?['severity']}**"
},
{
"title": "Created (UTC):",
"value": "@{triggerBody()?['object']?['properties']?['createdTimeUtc']}"
}
],
"separator": true
},
{
"type": "TextBlock",
"text": "[**View Incident in Sentinel Portal**](@{triggerBody()?['object']?['properties']?['incidentUrl']})",
"wrap": true,
"separator": true,
"weight": "Bolder",
"color": "Accent"
},
{
"type": "TextBlock",
"text": "Please choose an action for this incident:",
"wrap": true,
"separator": true,
"weight": "Bolder"
},
{
"type": "Input.ChoiceSet",
"id": "incidentAction",
"style": "expanded",
"value": "own",
"choices": [
{
"title": "Take Ownership",
"value": "own"
},
{
"title": "Dismiss as False Positive",
"value": "dismiss"
}
]
}
],
"actions": [
{
"type": "Action.Submit",
"title": "Submit Action"
}
]
}Step 4: The Logic - "Making Sense of the Response"
After the Teams action, we need to process the analyst's response.
1. Crack Open the Data with "Parse JSON"
Parse JSON: The response from the Teams card comes back as a single block of data (JSON). To make the individual pieces of information (like who clicked the button and which option they chose) usable, we first need to parse them.
- Click + New step and hunt down the Parse JSON action.
- In the Content field, the Logic App wants to know what to parse. Use the dynamic content picker and grab the Body from the "Post adaptive card and wait for a response" step above it.
- Now for the magic part, the Schema. This is the blueprint that describes the data. Don't panic and try to write this yourself. Click Use sample payload to generate schema and paste in the schema I've provided below. Or, just paste the schema directly into the box.
I am going to cover more about schemas in future posts, so don't forget to stay in touch!
{
"type": "object",
"properties": {
"responseTime": {
"type": "string"
},
"responder": {
"type": "object",
"properties": {
"objectId": {
"type": "string"
},
"tenantId": {
"type": "string"
},
"email": {
"type": "string"
},
"userPrincipalName": {
"type": "string"
},
"displayName": {
"type": "string"
}
}
},
"submitActionId": {
"type": "string"
},
"messageId": {
"type": "string"
},
"messageLink": {
"type": "string"
},
"data": {
"type": "object",
"properties": {
"incidentAction": {
"type": "string"
},
"incidentNumber": {
"type": "string"
}
}
}
}
}Nice, you've pasted that like a pro! Onto the next step..
2. Isolate the Good Stuff with "Compose"
Technically, you could pull directly from the Parse JSON step. But that's like leaving your tools scattered all over the floor. Real pros use the Compose action to create clean variables. It makes the playbook a thousand times easier to read and debug later.

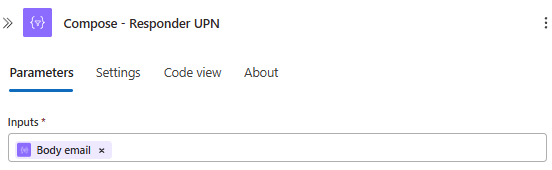
- Get the Responder:
- Add a new step and search for the Compose action.
- Click the three dots (...) on the action and Rename it to
Compose - Responder UPN. This is a pro-move. Do it. - In the Inputs field, use the dynamic content picker to find Body email from your Parse JSON step.
- Get the Action:
- Add another Compose step.
- Rename this one to
Compose - Incident Action. - For its Inputs, grab the Body incidentAction value from the Parse JSON step.
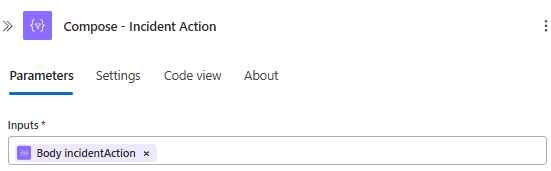
Look at that. Two clean, perfectly labeled variables. What a day to be alive

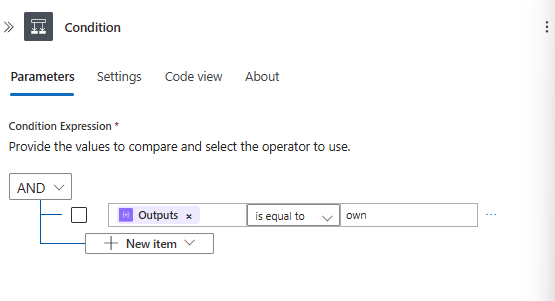
3. The Big Decision - Add a Condition
Now for the fork in the road. We need to check what the analyst actually clicked. Did they want to own the incident or dismiss it?
- Add a new step and choose the Condition control. This is your classic "if-then" statement.
- In the first box on the left, select Outputs from your
Compose - Incident Actionstep. See how nice and clean that is? - Set the operator in the middle to is equal to.
- In the box on the right, type own. This is the value we set in our Adaptive Card for the "Take Ownership" button.
Your playbook now has two paths: an "If true" branch (if they clicked "Take Ownership") and an "If false" branch.
4. The Payoff - Updating the Incident
This is what it's all been leading up to. Inside that glorious green If true box, we'll tell Sentinel to update the incident.
- Click Add an action inside the "If true" branch.
- Search for "Microsoft Sentinel" and choose the action Update incident.
- Fill out the fields like a boss:
- Incident ARM ID: Grab the Incident ARM ID from the original trigger at the very top.
- Status: Set this to Active.
- Owner: This is the magic moment. For the owner, select the Outputs from your
Compose - Responder UPNstep. - Add the permission part (at the very bottom), it's the same rule as in the initial trigger. Sign in with your account to create a connection.
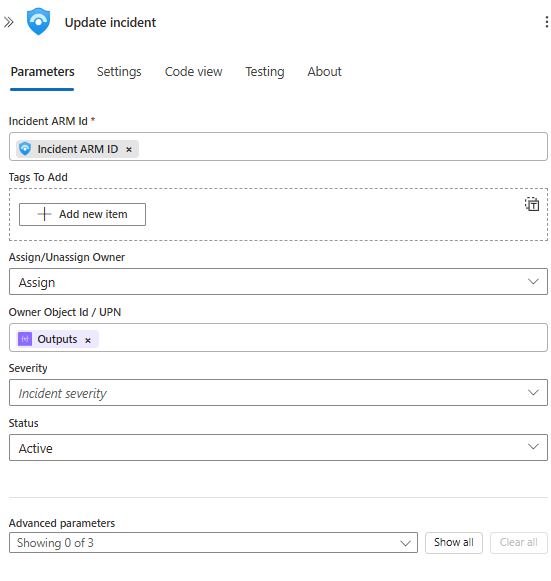
That's it. The incident will now be assigned to the exact person who clicked the button in Teams. Save your Logic App. You've earned it.
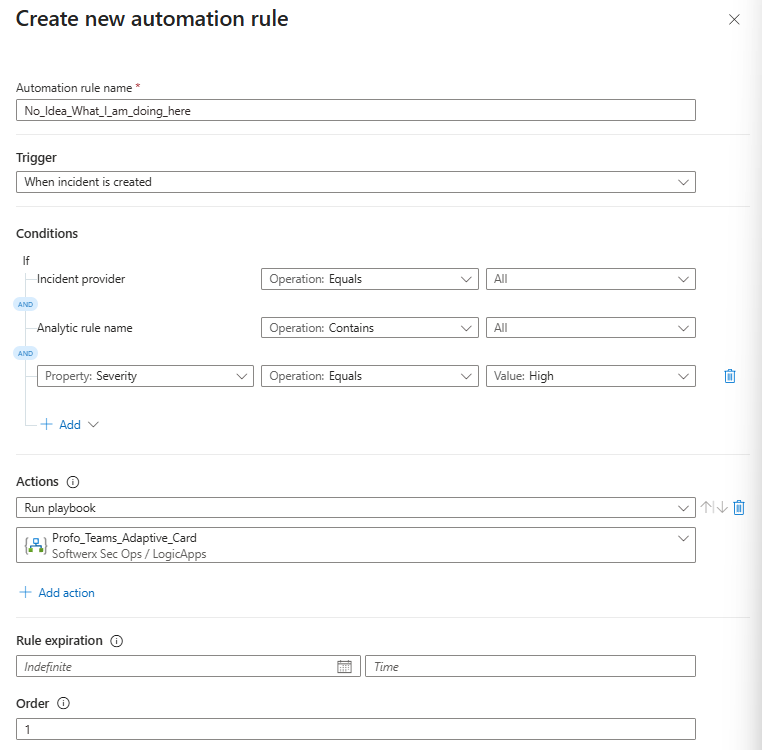
Step 5: Connect It, Test It, and Take the Credit
Let's wire this thing up and see it fly.
- Go back to Sentinel > Automation.
- Create a new Automation Rule.
- Give it a name that makes sense, like
Triage-High-Severity-Incidents-To-Teams. - Set the condition to If Severity contains High.
- Under "Actions," choose Run playbook and select the masterpiece you just created.
- Save it.
Now for the moment of truth! Fire off a test incident or just wait for a real high-severity alert to pop. A few seconds later, that beautiful, interactive card will appear in your Teams channel.
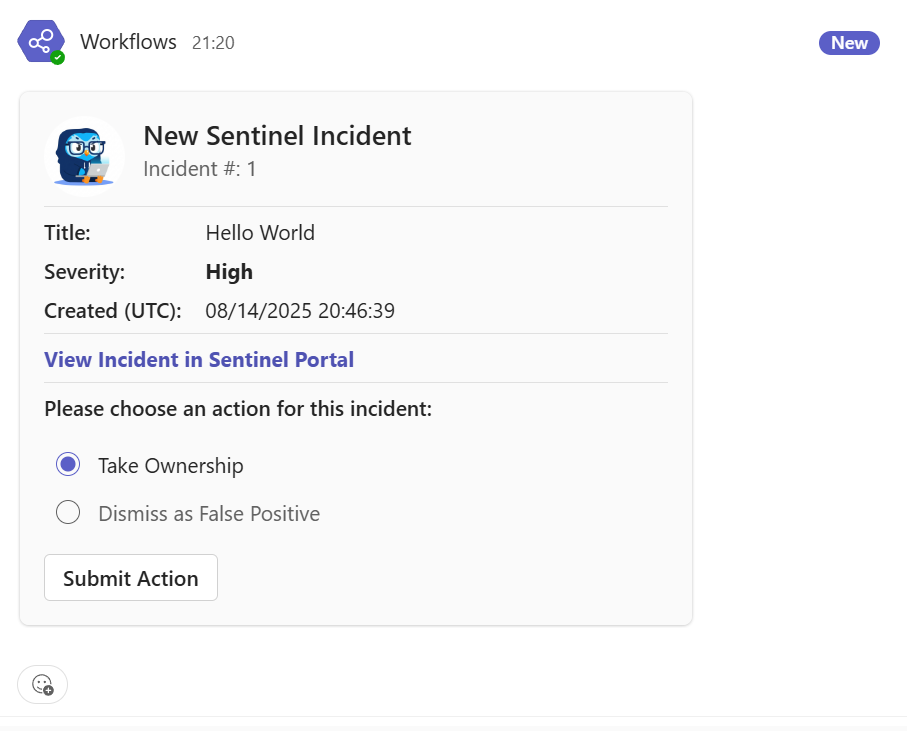
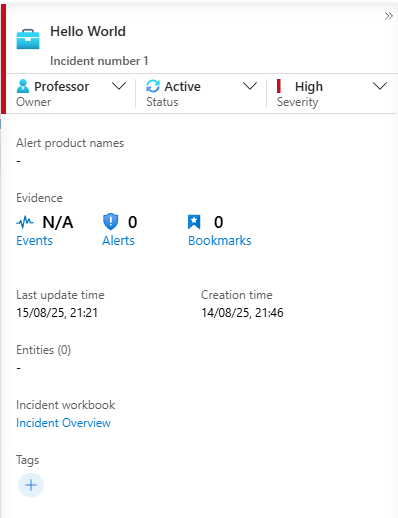
Go ahead, click "Take Ownership" and "Submit." Now, zip back over to your incident in Sentinel. You'll see the status is "Active" and the owner is... you.
You've just built a powerful automation that improves visibility, speeds up triage, and makes your team's life easier. You didn't just configure a tool; you solved a real-world operational problem. That, class, is what being a true security pro is all about. Now go show it off to your team.
